CHERI memory safety mitigates LLM-discovered vulnerability in FreeBSD

Brooks Davis – Capabilities Limited Over the past three weeks we’ve seen a number posts about the future of using LLMs for bug discovery and exploitation (https://www.forbes.com/sites/jonmarkman/2026/04/08/what-is-claude-mythos-and-why-anthropic-wont-let-anyone-use-it/, https://www.forbes.com/sites/amirhusain/2026/04/01/ai-just-hacked-one-of-the-worlds-most-secure-operating-systems/, https://blog.calif.io/p/mad-bugs-claude-wrote-a-full-freebsd). This has led to significant excitement in the popular press. It’s indisputable that new bugs are being found and rapidly exploited, but unclear if we’re seeing […]
Wind River Joins the CHERI Alliance

We are pleased to welcome Wind River to the CHERI Alliance, marking another important step forward in building a more secure computing ecosystem. Building on its existing work with CHERI, Wind River was recently awarded a contract as part of a strategic initiative led by Innovate UK and the Department for Science, Innovation and Technology […]
AI has compressed the attack timeline

Mike Eftimakis – CHERI Alliance Security by Design can’t wait! Recent news around advanced AI models has made one thing unmistakably clear: the pace of cyber exploitation has crossed a critical threshold. AI has reduced time-to-exploit so much that patching alone is no longer enough: we need security by design. Anthropic recently confirmed that its […]
ICENI: First Look
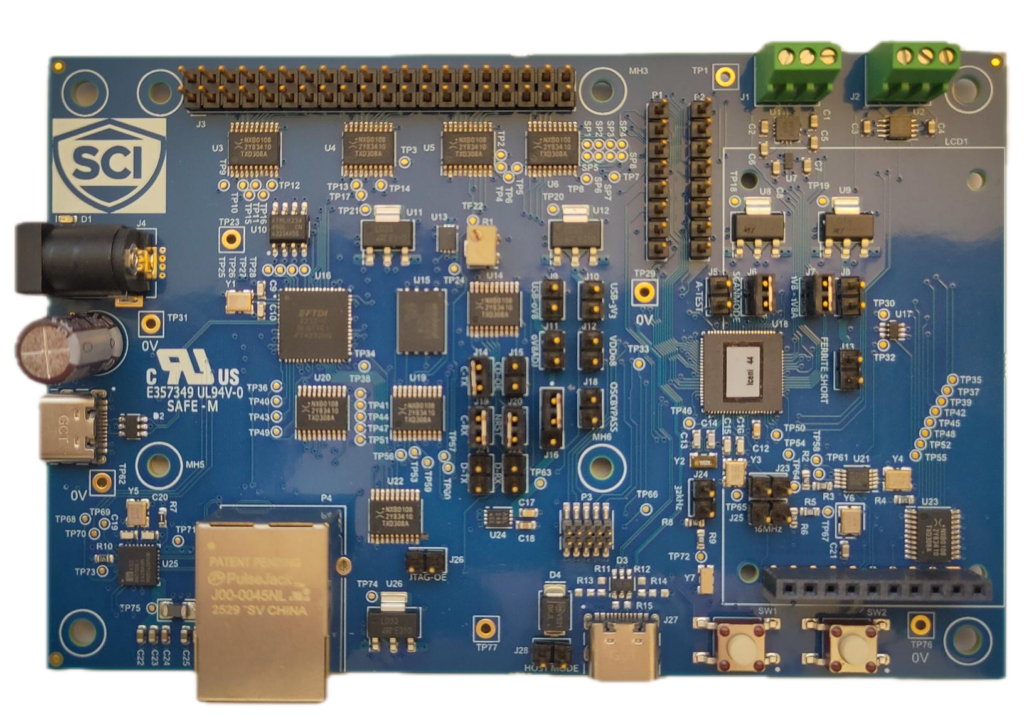
For more than a decade, CHERI research has demonstrated that hardware enforced memory safety can eliminate entire classes of security vulnerabilities. Much of this work has taken place in simulators and FPGA platforms, enabling researchers and developers to experiment with capability based architectures before production hardware became available. The CHERIoT project extends these principles to […]
The Capable Hub joins the CHERI Alliance to accelerate cybersecurity collaboration

Strengthening the CHERI ecosystem through Open-Source innovation We are excited to announce that The Capable Hub has become a member of the CHERI Alliance, a significant step forward in our mission to accelerate CHERI adoption. Improving the availability, quality, and upstream alignment of CHERI-enabled open-source software will make the design of CHERI-secured products easier and […]
The EU Cyber Resilience Act: What It Means for Secure-by-Design Systems and CHERI

In 2025 alone, global cybercrime costs reached an estimated $1.2 billion every minute, with projections rising to $1.8 billion per minute by 2029. Just seven years earlier, the figure was “only” $100 million per minute—already enormous, but now eclipsed by today’s scale.
Amid rising cyber threats, EnSilica joins the CHERI Alliance to enable safe & secure silicon

Oxford UK – 3 February 2026 – EnSilica, a leading provider of mixed-signal ASICs (Application-Specific Integrated Circuits), today announced that it has joined the CHERI Alliance. In a world facing an explosion of cyber threats, this collaboration will accelerate the adoption of a technology that could eliminate more than 70% of current vulnerabilities. The Power of […]
Towards a reference QEMU for CHERI platform emulation
Alfredo Mazzinghi – Capabilities Limited QEMU is one of the most popular open source machine emulators (https://www.qemu.org), with support for many CPU architectures, including x86_64, Arm and RISC-V. The QEMU emulator is critical for systems research and development: it makes it possible to quickly prototype, debug and analyse architectural extensions and OS implementations without the […]
Codasip Powers UK Digital Security by Design Innovation Contracts with CHERI Technology
Andrew Lindsay – Codasip Codasip’s CHERI-RISC-V processors and exploration kit enable breakthrough secure chip development and accelerate software innovation The UK government’s ambitious Digital Security by Design initiative continues to gain momentum, with Codasip playing a pivotal role in two key innovation contracts announced as part of the program’s £21 million investment to advance hardware-based […]
CHERI or CHERIoT? The Answer Is Not What You Think

Adam Finney – CHERI Alliance Interest in capability based security has grown rapidly as organisations look for practical ways to move beyond legacy memory protection. As more projects explore CHERI technologies, a common question keeps surfacing: should we use CHERI or CHERIoT? At first glance it sounds like a straightforward architectural decision, but as David […]
