Introducing the CHERI Adoption Global Ecosystem Assessment Q1 2026
In 2025 alone, global cybercrime costs reached an estimated $1.2 billion every minute, with projections rising to $1.8 billion per minute by 2029. Just seven years earlier, the figure was “only” $100 million per minute—already enormous, but now eclipsed by today’s scale.
One Bug is All It Takes

In 2025 alone, global cybercrime costs reached an estimated $1.2 billion every minute, with projections rising to $1.8 billion per minute by 2029. Just seven years earlier, the figure was “only” $100 million per minute—already enormous, but now eclipsed by today’s scale.
Why Codasip went all‑in on CHERI

Interview with Ron Black, CEO of Codasip Codasip is a founding member of the CHERI Alliance and one of the most active industrial players in the CHERI ecosystem. From the outset, Codasip has played an active role in CHERI Alliance activities—taking part in technical discussions, leading some working groups, contributing open-source software, supporting standardisation efforts, […]
CHERI memory safety mitigates LLM-discovered vulnerability in FreeBSD

Brooks Davis – Capabilities Limited This article is part of a series of blogs published after the announcement of Mythos vulnerabilities’ exploitation capabilities. The views from other experts on this topic are: AI has compressed the attack timeline – Mike Eftimakis One Bug is All It Takes – Adam Finney Over the past three weeks […]
Wind River Joins the CHERI Alliance

We are pleased to welcome Wind River to the CHERI Alliance, marking another important step forward in building a more secure computing ecosystem. Building on its existing work with CHERI, Wind River was recently awarded a contract as part of a strategic initiative led by Innovate UK and the Department for Science, Innovation and Technology […]
AI has compressed the attack timeline

Mike Eftimakis – CHERI Alliance This article is part of a series of blogs published after the announcement of Mythos vulnerabilities’ exploitation capabilities. The views from other experts on this topic are: CHERI memory safety mitigates LLM-discovered vulnerability in FreeBSD – Brooks Davis One Bug is All It Takes – Adam Finney Security by Design […]
ICENI: First Look
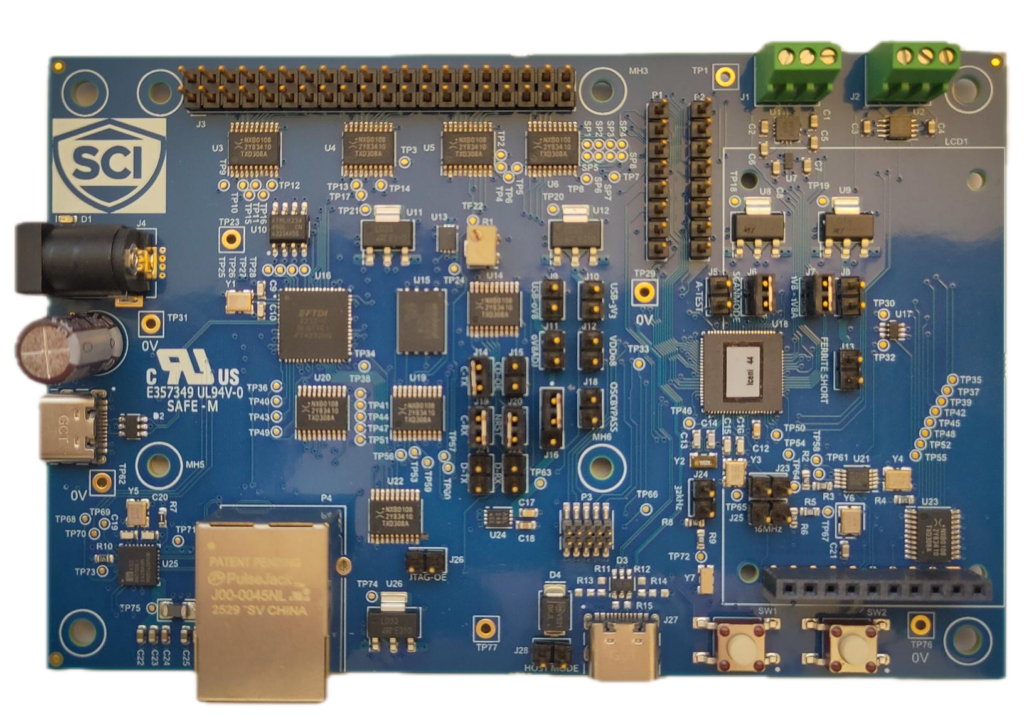
For more than a decade, CHERI research has demonstrated that hardware enforced memory safety can eliminate entire classes of security vulnerabilities. Much of this work has taken place in simulators and FPGA platforms, enabling researchers and developers to experiment with capability based architectures before production hardware became available. The CHERIoT project extends these principles to […]
The Capable Hub joins the CHERI Alliance to accelerate cybersecurity collaboration

Strengthening the CHERI ecosystem through Open-Source innovation We are excited to announce that The Capable Hub has become a member of the CHERI Alliance, a significant step forward in our mission to accelerate CHERI adoption. Improving the availability, quality, and upstream alignment of CHERI-enabled open-source software will make the design of CHERI-secured products easier and […]
Amid rising cyber threats, EnSilica joins the CHERI Alliance to enable safe & secure silicon

Oxford UK – 3 February 2026 – EnSilica, a leading provider of mixed-signal ASICs (Application-Specific Integrated Circuits), today announced that it has joined the CHERI Alliance. In a world facing an explosion of cyber threats, this collaboration will accelerate the adoption of a technology that could eliminate more than 70% of current vulnerabilities. The Power of […]
Codasip Powers UK Digital Security by Design Innovation Contracts with CHERI Technology
Andrew Lindsay – Codasip Codasip’s CHERI-RISC-V processors and exploration kit enable breakthrough secure chip development and accelerate software innovation The UK government’s ambitious Digital Security by Design initiative continues to gain momentum, with Codasip playing a pivotal role in two key innovation contracts announced as part of the program’s £21 million investment to advance hardware-based […]
